Table of Contents
← Hide Table of Contents
 MIDAS SSO: Microsoft Entra ID (Azure AD)
MIDAS SSO: Microsoft Entra ID (Azure AD)
This guide explains how to configure Microsoft Entra ID as a SAML Identity Provider (IdP) for MIDAS, allowing users to sign in using their Microsoft corporate accounts.
What you'll need before starting
- Admin access to Microsoft Entra ID
- Admin access to MIDAS
- MIDAS Unlimited Users licence
- A test user account in Entra ID with a valid email address
Overview of the process
- Create a SAML application in Entra ID
- Configure SAML settings (Entity ID, ACS URL, claims)
- Download the Entra ID signing certificate
- Configure SAML settings in MIDAS
- Assign users and test login
Step 1 - Create the application in Entra ID
- Sign in to the Microsoft Entra admin center
- Go to Enterprise applications
- Click New application
- Select Create your own application
- Enter a name, e.g. MIDAS SSO
- Choose Integrate any other application you don't find in the gallery (Non-gallery)
- Click Create
Step 2 - Enable SAML single sign-on
- Open the newly created MIDAS SSO application
- Select Single sign-on
- Choose SAML
Step 3 - Configure Basic SAML settings
The "Set up Single Sign-On with SAML" page contains numbered sections: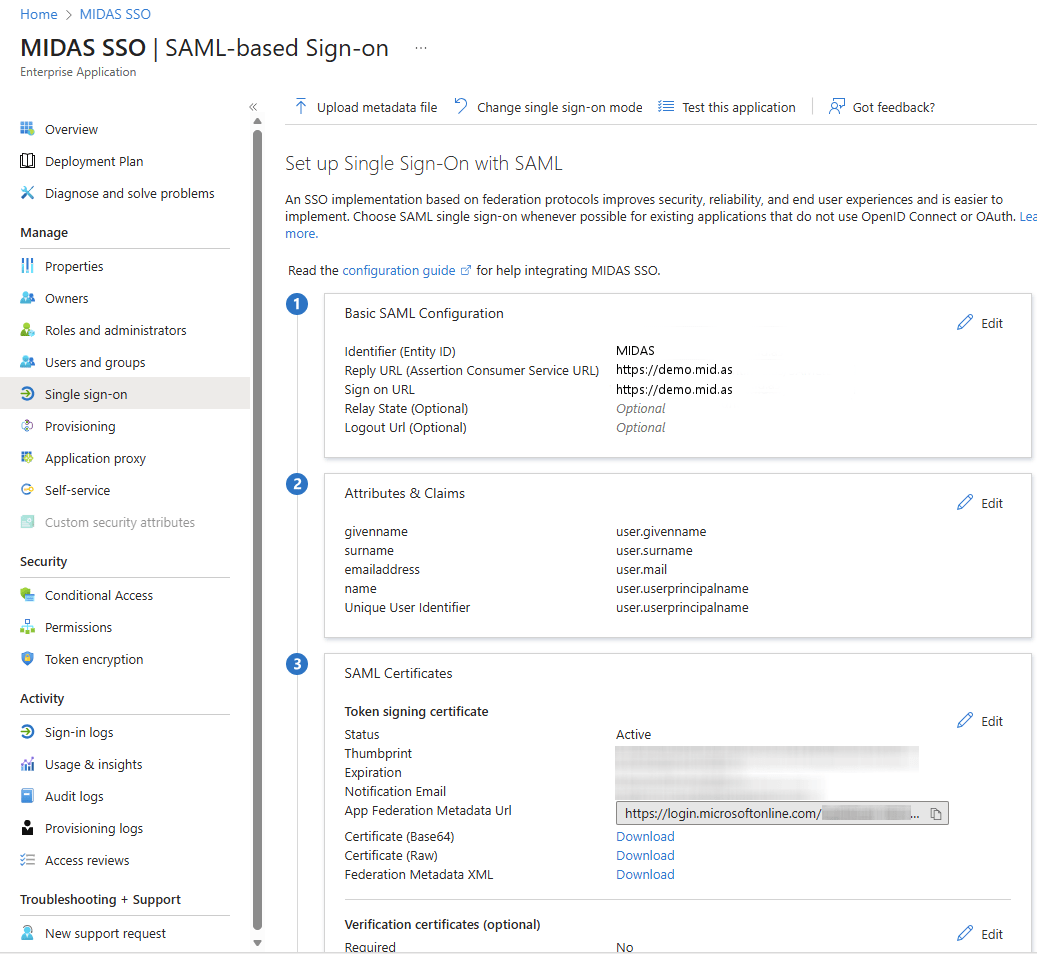
| Field | Value |
| Identifier (Entity ID) | MIDAS |
| Reply URL (ACS URL) | The URL of your MIDAS system i.e. https://demo.mid.as If testing using our SAML Test Tool, use the URL to the tool instead i.e. https://demo.mid.as/SAMLtest.pl |
| Sign-on URL | The URL of your MIDAS system i.e. https://demo.mid.as If testing using our SAML Test Tool, use the URL to the tool instead i.e. https://demo.mid.as/SAMLtest.pl |
Step 4 - Check Attributes & Claims
MIDAS identifies users by email address. It is therefore important to check that an authenticated user's email address (i.e. "user.mail") is passed back to MIDAS, as well as the user's name (for example, "user.givenname" and "user.surname").Step 5 - Download the SAML signing certificate
- In the SAML Signing Certificate section
- Download the Base64 certificate
- Save it securely - you'll upload this to MIDAS
Step 6 - Assign users or groups
- Open Users and groups
- Assign:
- Individual users or
- A security group (recommended)
Only assigned users will be able to sign in to MIDAS using SSO.
Step 7 - Configure SAML SSO in MIDAS
In MIDAS:- Go to Admin → Manage Users & Permissions → Single Sign-On (SSO)
- Select SAML 2.0
- Enter the following in the Identity Provider Settings section:
- Metadata - Enter the "App Federation Metadata URL" provided by Entra ID. Alternatively, in Entra ID you can download "Federation Metadata XML", and then copy and paste the contets of that file into this field.
- Certificate - copy and paste the contents of the Base64 certificate you downloaded from Entra ID
The Service Provider Settings section in MIDAS can be left blank, as it is not used by Entra ID.
In the MIDAS Settings section, select a default permissions group for new users using the "Assign users permissions from" drop-down, and Save Changes.Step 8 - Test the login
Option A: Entra ID test- Use Test in the Entra ID SAML screen
- Visit your MIDAS SSO login URL
- Sign in with an assigned Entra ID user
A successful sign-in confirms that integration is working.
 MIDAS SSO: Microsoft Entra ID (Azure AD)
MIDAS SSO: Microsoft Entra ID (Azure AD)